PRODUCTS
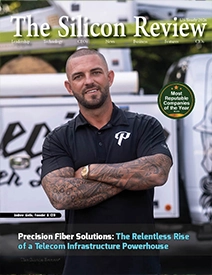 Most Reputable Companies of the Year 2026
Most Reputable Companies of the Year 2026
 June Monthly Edition 2026
June Monthly Edition 2026
 June Edition 2026
June Edition 2026
 May Monthly Edition 2026
May Monthly Edition 2026
 May Edition 2026
May Edition 2026
 April Monthly Edition 2026
April Monthly Edition 2026
© 2026 Silicon Review LLC. All Rights Reserved.